by PCS | Dec 19, 2024 | 2024, Tips & Tricks
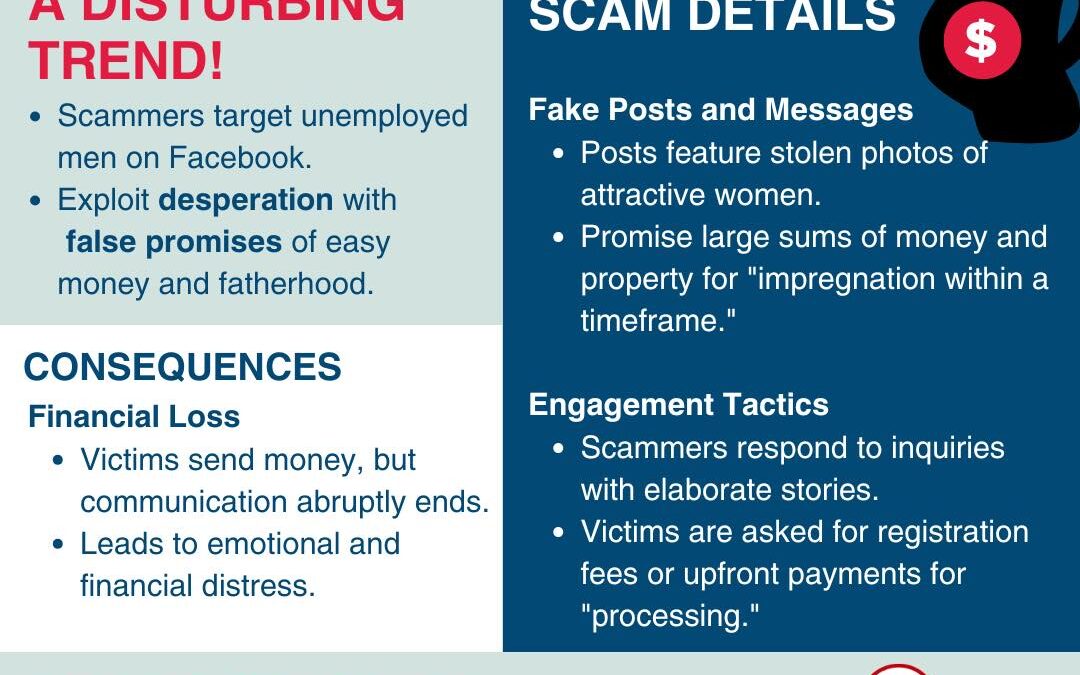
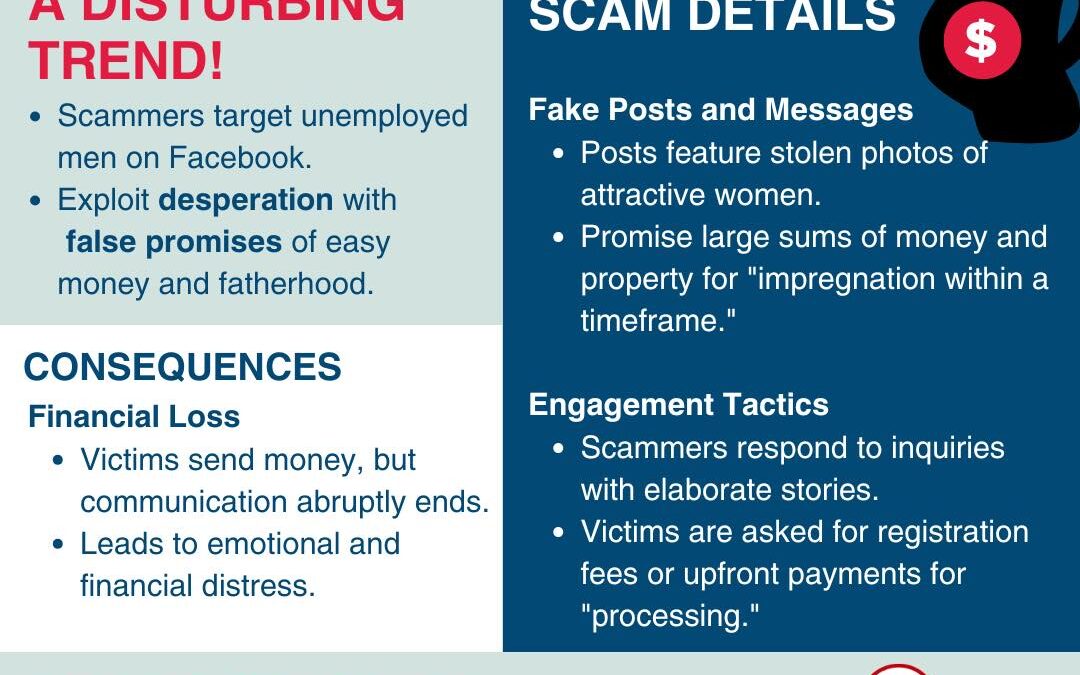
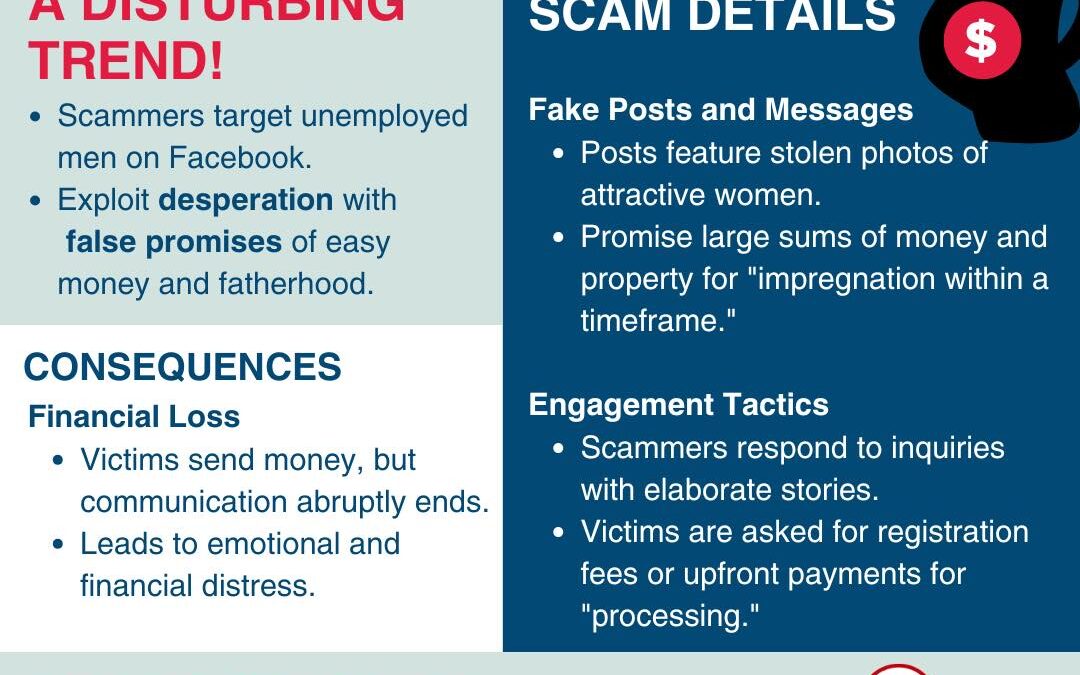
A new scam on Facebook is targeting unemployed men with false promises of lucrative rewards in exchange for fatherhood. These scams lure victims with stolen photos and elaborate stories, ultimately extracting upfront payments before disappearing. Never trust...
by PCS | Dec 19, 2024 | 2024, Tips & Tricks
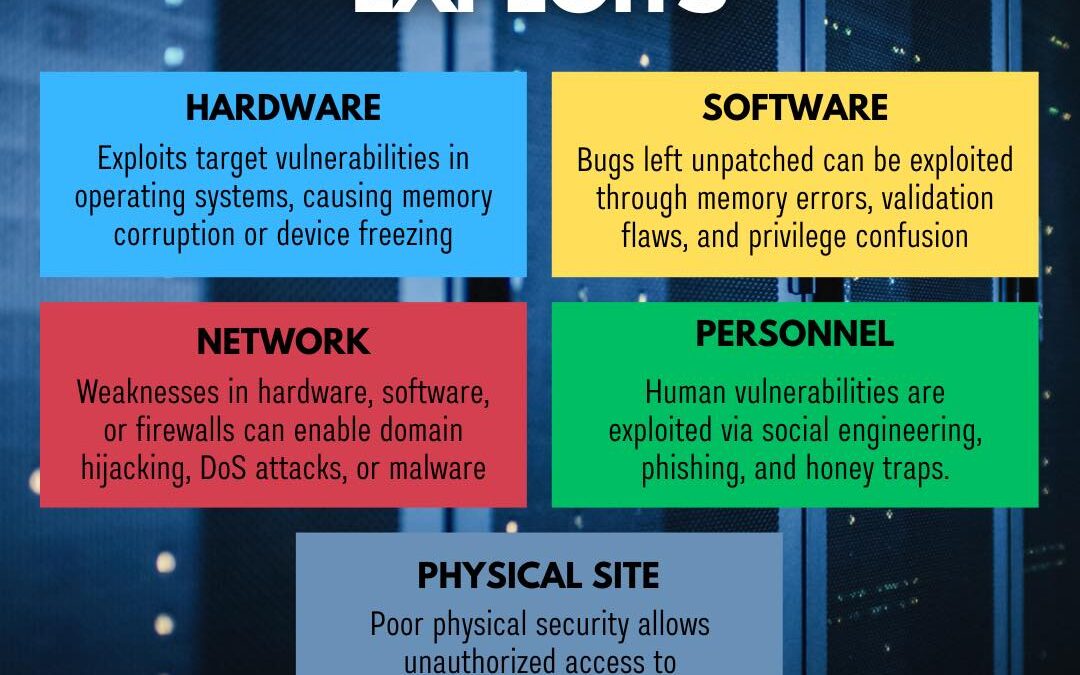
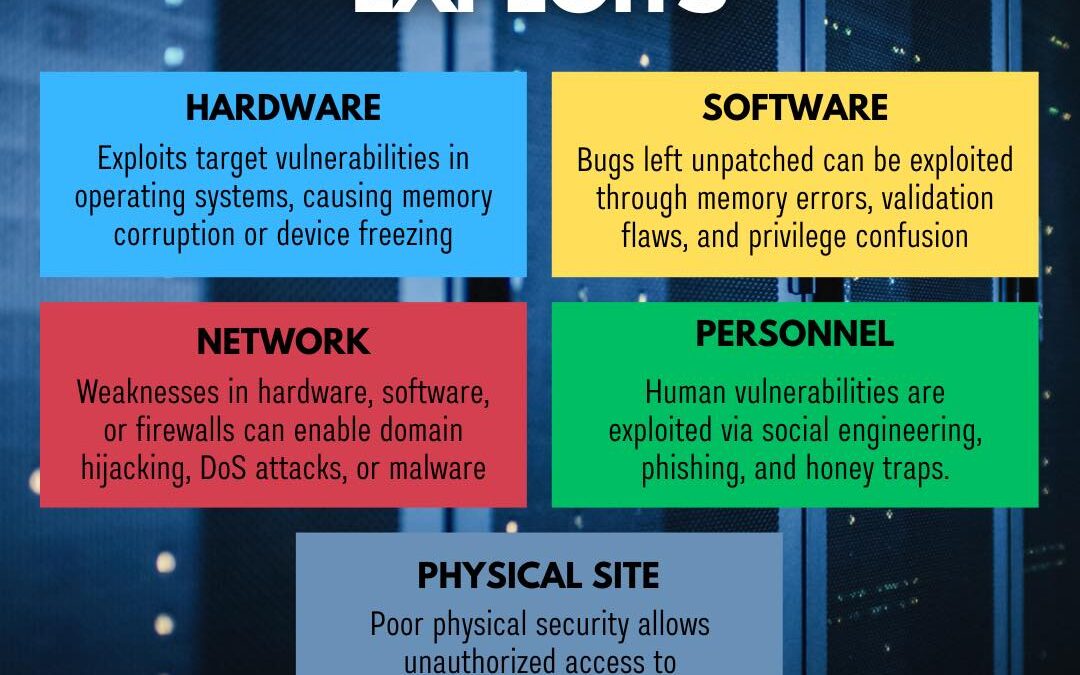
Understanding the different types of cyber exploits is the first step in safeguarding your organization. From hardware vulnerabilities and software bugs to network gaps, personnel manipulation, and physical site breaches, cybercriminals are always on the lookout for...
by PCS | Dec 19, 2024 | 2024, Tips & Tricks
Exploits are a critical tool in the hacker’s arsenal, taking advantage of software or hardware flaws to infiltrate and compromise systems. While they’re often confused with malware, exploits are the methods, not the payloads; they’re the doors left ajar that allow...

by PCS | Dec 19, 2024 | 2024, Tips & Tricks
Protecting your digital privacy can be simple with the right steps. These quick tips can help you keep your online activities and personal data safe. #PinedaCyberSecurity #CyberSecurityMakesSenseHere #DigitalPrivacy #StaySafeOnline #PrivacyMatters #SafeBrowsing...

by PCS | Dec 19, 2024 | 2024, Tips & Tricks
Staying safe online is essential, especially for teenagers who often use social media and apps. Small actions like managing app permissions, setting accounts to private, and using secure messaging tools can significantly reduce privacy risks. Simple adjustments lead...
by PCS | Dec 19, 2024 | 2024, Tips & Tricks
Acting as a digital barrier, a firewall defends networks from unauthorized access, allowing only trusted data to pass through. Positioned between a trusted network and potential threats from external networks, it scrutinizes every data packet that attempts to enter or...